MeXT-SE: Multi-Processor System-on-Chip (MPSoC) Exploration with Security Extension
Overview
The Multi-processor System-on-Chip (MPSoC) Exploration with Security Extension (MeXT-SE) is an SoC development tool. MeXT-SE can generate platform-independent secure multi-processor systems from a high-level abstraction. The architecture of the secured multi-processor system is designed based on the extension of the Flask security architecture. The goal of this project is to provide users a flexibility to design a secured MPSoC. The brief description of the secured system, the tool design flow and tool resources are given below.
Secured System-on-Chip

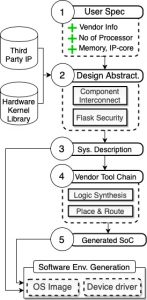
Figure 1 shows the target system-on-chip sought to be generated by mext and operate safely. The tool starts with a user-defined abstract and concrete representation (XML format) of a system and ends up generating a final hardware design with enforced countermeasures for preventing unauthorized access of hardware IPs in the SoC. While setting up the communication network, an access control mechanism that inherits MAC-based authentication policies, found in the flask security architecture, is enforced directly in the hardware design. The architecture of the generated system is shown in figure. The flask security framework is implemented as a decentralized hardware/software architecture with the Hardware IP Management Module (HIMM) that governs access control at the IP level, while the Software IP Management Module (SIMM) manages policies inheritance of security contexts and queries the host kernel security server for associated permissions.
The HIMM consists of an internal enforcement function and an Access Vector Cache component (AVC) to cache the last queries and ensure that policies check are handled locally. Each HIMM maintains a map of security context labels for the corresponding hardware module it manages. It implements a custom circuit, the “Access Enforcement Function,” which guards access to the hardware modules according to the host kernel MAC policy. Upon receiving an access request to the hardware module, the SIMM module on the host CPU queries the host kernel security server for associated permissions. The server consults its MAC policy and returns associated permissions, which are then sent to the respective HIMM module for future access requests. The detail about the security framework can be found in references [1,2,3].
MeXT-SE Design Flow
This section describes a brief overview of the design flow of MeXT-SE. The user will provide abstract and concrete specifications of a system such as the number of processors, memory size, hardware IPs, operating system, target device, etc. The tool uses this knowledge to generate the appropriate hardware design script for the required vendor. The input to MeXT-SE is an XML file with abstract specification and the tool generates a platform-specific tcl script that can be directly run on Vendor tools (e.g. Xilinx Vivado, Intel Quartus, Accellera SystemC) to generate a bitstream. While generating the hardware design, MeXT-SE enforces the flask security framework to govern access control between components of different security domains. This feature is imposed transparently to the design to ensure security on the generated SoC. The tool also generates the script required to create embedded operating system for the vendor specific board.
MeXT-SE resources
MeXT-SE can be dowloaded from the following github link. A documentation is present in the repository which describes the system requirement to run the tool and the usage of the tool.
https://github.com/smartsystemslab-uf/MeXT-SE
References
- Md Jubaer Hossain Pantho and Christophe Bobda. 2020. MeXT-SE: A System-Level Design Tool to Transparently Generate Secure MPSoC. 28th IEEE International Symposium on Field-Programmable Custom Computing Machines (FCCM), Fayetteville, AR, USA
- F. Hategekimana, Joel Mandebi Mbongue, Md Jubaer Hossain Pantho, and Christophe Bobda. 2018. Inheriting Software Security Policies Within HW IP Components. 26th IEEE International Symposium on FieldProgrammable Custom Computing Machines (FCCM), Boulder, CO, USA
- F. Hategekimana, Joel Mandebi Mbongue, Md Jubaer Hossain Pantho, and Christophe Bobda. 2018. Secure Hardware Kernels Execution in CPU+FPGA Heterogeneous Cloud. 2018 International Conference on FieldProgrammable Technology (FPT), Naha, Okinawa, Japan
Contributors




Sponsor
